Automation-first SOC portfolio, repo-backed and verifiable.
I build deployable detections and response workflows with repeatable validation and measurable outcomes, because that's where modern security operations is heading.
Review path: open Proof Pack, run verify, match published outputs.
pwsh -File .\scripts\verify\verify-counts.ps1
raylee-hawkins/HawkinsOperations (verified, reproducible today).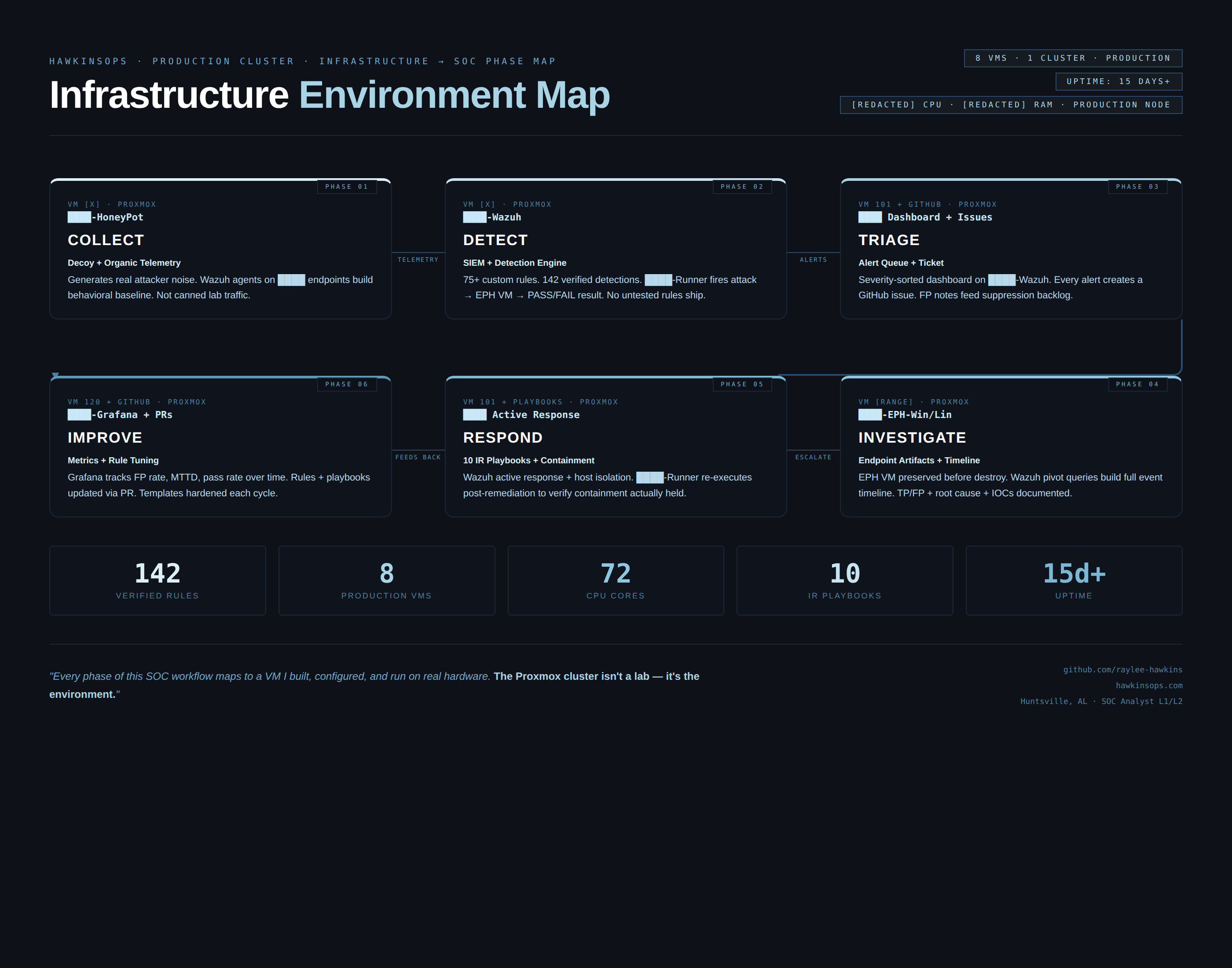
Choose your verification lane
Pick the reviewer path you need. Every lane ends with reproducible artifacts.
Self-taught. No degree. Everything verified.
Self-taught North Alabama security engineer. Every count on this site is reproducible with a single command against a public repo—because claims without proof aren't claims at all.
I chose the automation side of security because that's where modern SOC operations is heading. The goal isn't just detection—it's detection you can reproduce, explain, and hand off.
A workflow-shaped SOC portfolio
HawkinsOps is a security operations portfolio built like a real workflow: collect telemetry, detect, triage, respond, investigate, and improve.
- Wazuh agent on a primary Windows 11 endpoint wired to Proxmox-hosted Wazuh Manager and Splunk
- 139 verified detections active across Sigma, Wazuh, and Splunk
- Detection scenarios run end-to-end: trigger → alert → evidence capture → verify counts
pwsh -NoProfile -File .\scripts\verify\verify-counts.ps1 pwsh -NoProfile -File .\scripts\verify\generate-verified-counts.ps1 -OutFile .\PROOF_PACK\VERIFIED_COUNTS.md
Report-first, repo-last
Short case studies, lab briefs, and detection reports. Each section explains what the rule/workflow does, the purpose it serves, and ends with artifacts plus a verification path.