CVE-2025-55130: detected by Wazuh, triaged, patched, and verified closed in one operational cycle
Critical Node.js vulnerability surfaced during routine SOC monitoring — not from a scanner run on a schedule, but from Wazuh's vulnerability detection module running continuously against monitored endpoints. The full response loop: detection → triage → investigate → patch → verify. Evidence at every step.
Context
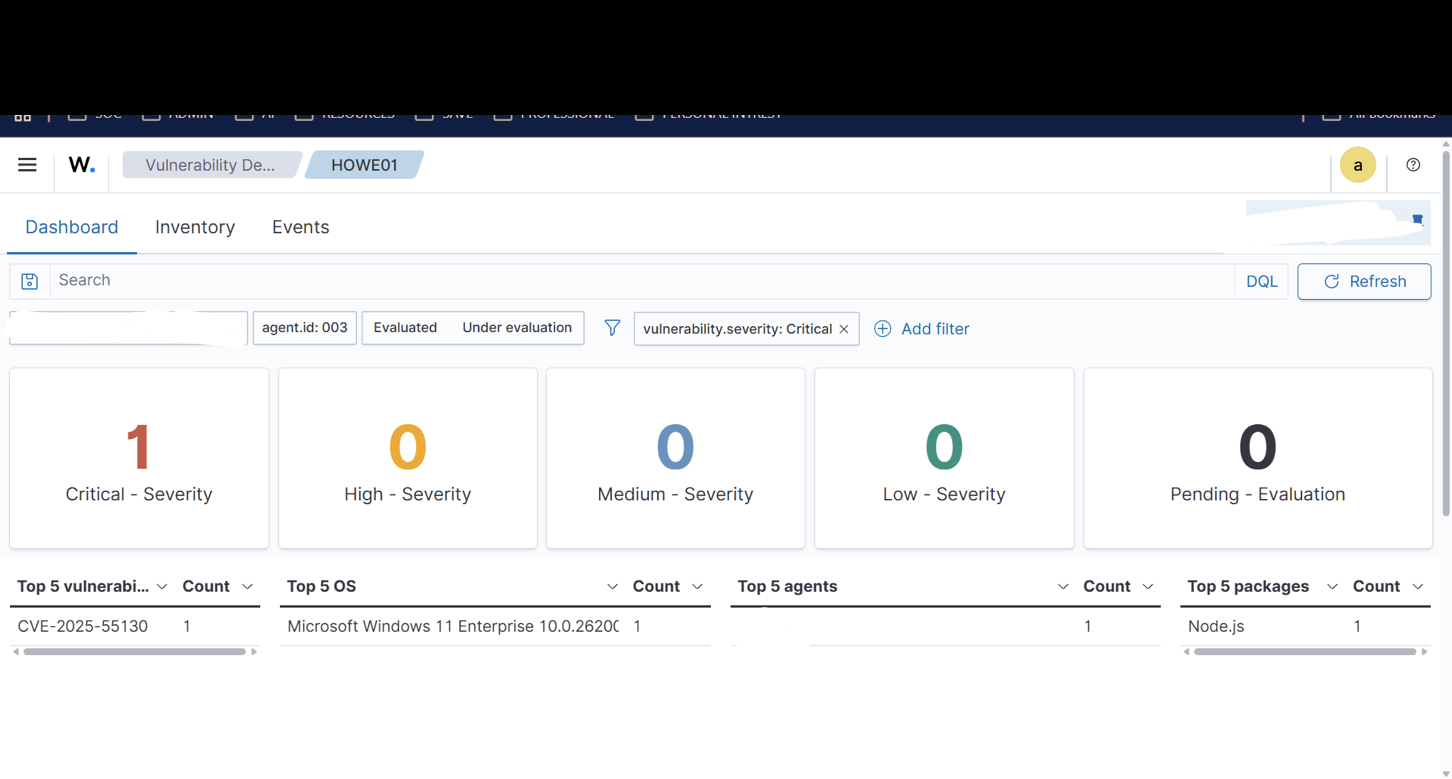
Wazuh's vulnerability detection module flagged CVE-2025-55130 (critical severity, Node.js LTS) on a monitored Windows endpoint during the PP_SOC_Integration monitoring window. The finding appeared in the vulnerability summary dashboard alongside 31 high-severity findings. Before this detection, the critical count was 0 — this CVE was the first critical finding to surface.
- CVE: CVE-2025-55130
- Package: Node.js LTS (OpenJS.NodeJS.LTS)
- Severity: Critical
- Detection source: Wazuh vulnerability detection module (not a scheduled scan)
- Context: Discovered during active 24-hour monitoring window (15,052 alerts observed)
Problem
- Confirmed CVE is critical (not a false positive flagging dev tooling in an isolated context).
- Identified affected package: Node.js LTS on a production-sim Windows endpoint under active Wazuh monitoring.
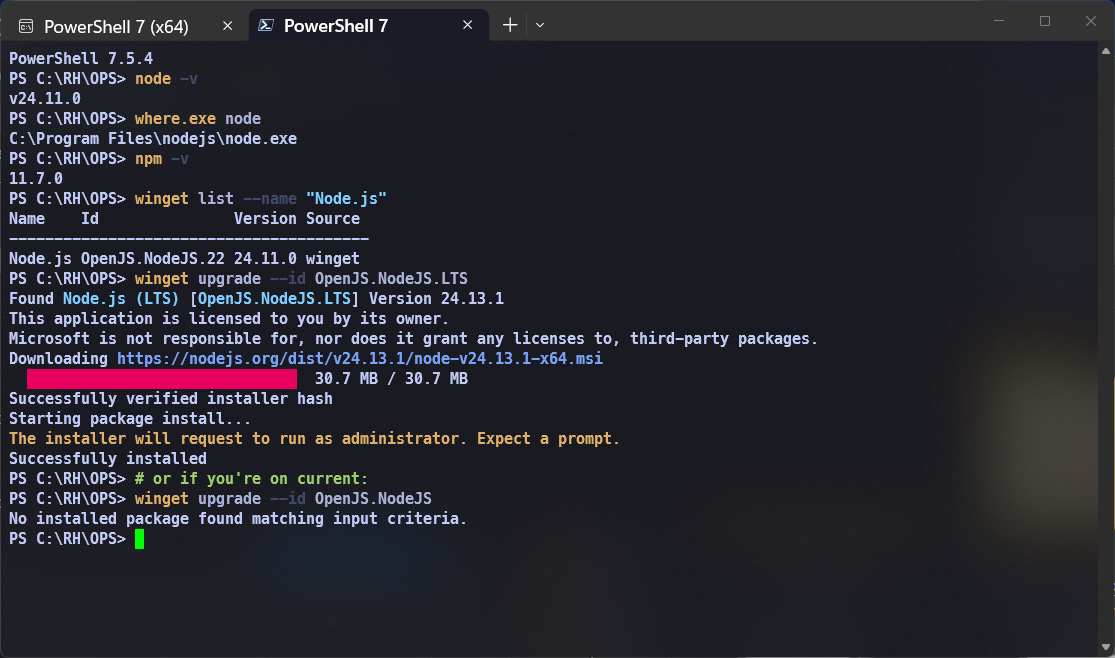
- Confirmed package path via
winget list --name "Node.js"— version string matched vulnerable range. - Patch available: winget upgrade target identified.
- Decision: patch in-cycle, not deferred. Critical finding in an active monitoring environment does not queue.
Approach
Single-command patch execution:
winget upgrade --id OpenJS.NodeJS.LTS
Verification commands run after upgrade:
node -v winget list --name "Node.js"
Post-patch: Wazuh service health confirmed after upgrade and restart. Agent connectivity verified.
Evidence
Terminal output captured showing upgrade completion and version confirmation.
Outcome
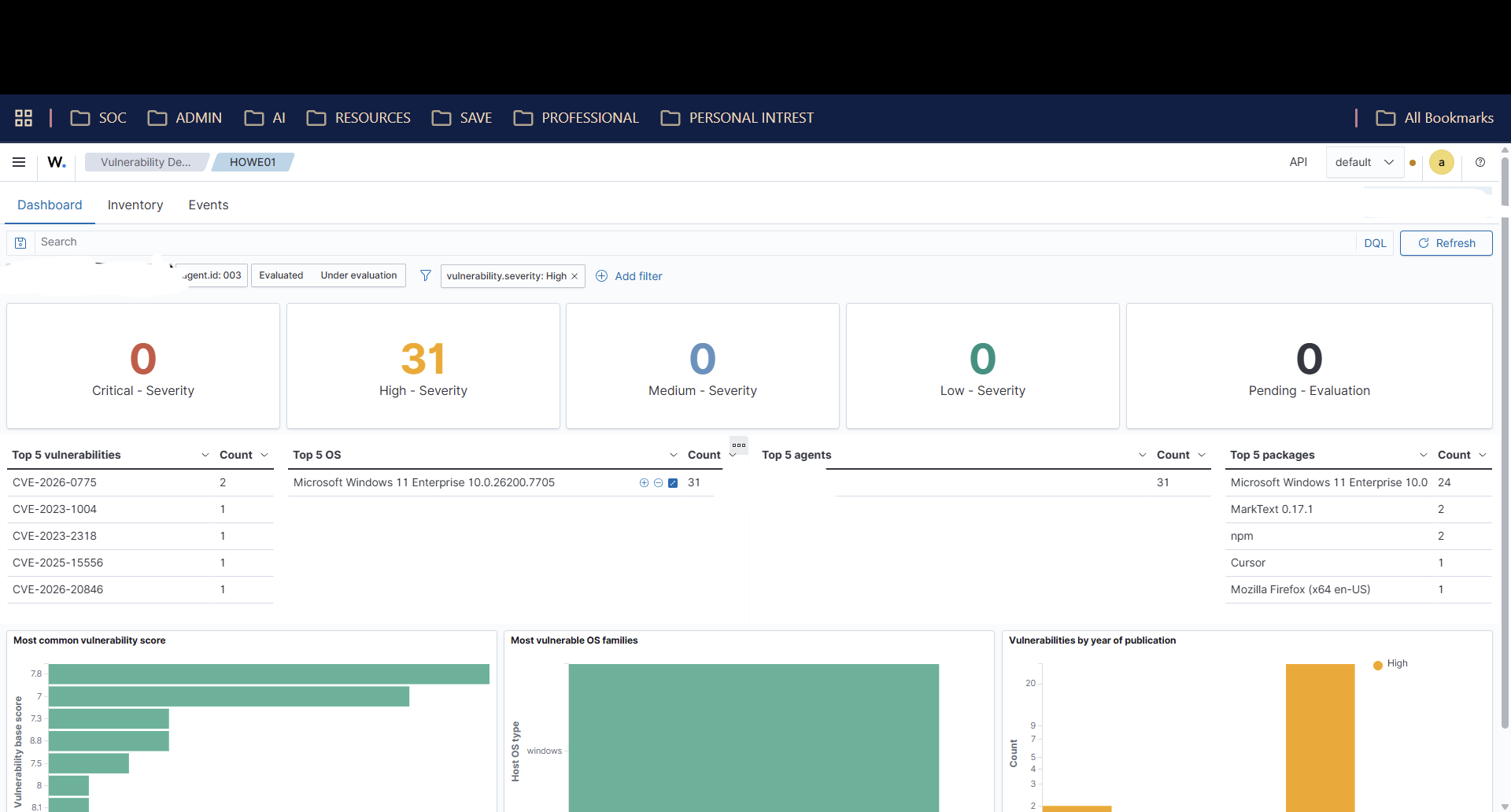
After patch and Wazuh service restart:
- CVE-2025-55130 no longer appears in vulnerability findings.
- Vulnerability summary: 0 critical, 31 high (pre-existing, prioritized queue).
- Agent connectivity and alert streaming confirmed operational.
- Finding closed in-cycle — no deferred remediation queue entry created.
Lessons + next hardening step
- Continuous monitoring pays off — this finding was not from a scheduled quarterly scan. Wazuh surfaced it during normal monitoring operation.
- Detect-to-patch in one cycle — no deferred queue, no "we'll fix it next sprint." Critical finding → patch decision → execute → verify.
- Evidence at every step — detection screenshot, patch terminal output, post-remediation state captured.
- Wazuh vulnerability detection module provides CVE coverage as a continuous operational input, not a periodic report.
Next hardening step
- Lab environment — production remediation would require change control and rollback validation steps not present here.
- Screenshots contain internal hostnames and identifiers; all are redacted per
PROOF_PACK/EVIDENCE_CHECKLIST.mdpolicy. - Single-package patch — this is a point remediation, not a complete vulnerability management program.